
Secure your infrastructure in one lecture
Once your devices are exposed to the internet, you start worrying about how to maintain and secure your infrastructure. Get better sleep at night knowing you have done everything possible to keep your data safe from threats.
This is a post suitable for anybody who has services running on the internet.

Secure your Linux distribution
The idea is to connect for the first time using a secure shell and have all the initial traffic encrypted.
Most data centers offer the option to upload a secure key and be installed as soon as the operating system is built. Once this is done you can install another key that is going to replace the one you sent to the data center site. This is true for VPS and Dedicated servers.
Once your operating system is ready, another big step must be done for safety. We call it hardening your operating system. This is basically applying initial rules to make your system more secure.
- Disable direct root login: meaning no one is able to use a root user for login. The only possible choice is to use a secure key. Do not worry, you can log in using a root password but from a secure console; similar to having the keyboard and screen connected to the server. This remote console is secure and only you can access the terminal through the data center control panel.
- Create a Wheel user: this is a bogus user with low privileges, something like "myuser15", or "secure101". Make the name of the user something unique and not something that anybody can guess. Once you create the user make him part the wheel. This will allow you to switch to root using a password only after logging in using SSH with a secure key. The process is like this:
- Use the SSH with a key to log in using a "secure101" user, a user with a nonstandard name and low privilege.
- Once you are inside the shell, you switch to root user using the specific "Sudo" command and write the root password when requested.
- Only after that, you do have full rights as administrator. Do you see how this makes things hard for unauthorized users?. That is the idea.
- Use strong passwords: no matter that you are using SSH keys, as a general rule always use strong passwords for standard users and applications that require it. It is better to combine numbers, letters, and special characters. This is one way to protect against brute force attacks.
- Change the default SSH port number: everybody knows the standard port for SSH is 22, so let's make it a different number. For that, you would need to review the list of most common ports and pick up something that is not there. Do not use anything that other services will use, like port 20 or 21 as they are for FTP; or port 80 as this is an HTTP protocol. You can check Wikipedia for a good list. Pick up something in the thousand range, like 3230 or 152o.
- Enable and configure your firewall: these are rules that allowed specific traffic to come and go to your server. As a general rule, you would block everything and allow only the knowing ports that your services are running. In this way, there won't be any application popping up and trying to use a port when it is not allowed.
Steps 1 to 5 will cover only the first and the basic security of any Linux distribution, similar can be done for any Microsft Windows Server located at the border of the abysm called the internet.
Secure by Hardening your Hosting Control Panel
It is up to you if you want to use a vanilla implementation and install manually all your services, or do what I recommend which is to use a web-based control panel like cPanel, Webmin, Webuzo, or any other. The idea is to facilitate the administration of your server or VPS, this is done through an easy-to-use graphical interface based on a web browser.
It is much easier and less time-consuming to click a check box than run a command line using SSH. Web Hosting Control Panel works perfectly not only for web hosting companies but for single users and definitely It will make your life easier.
There are all kinds of control panels, some of them are open source and free to use and some others have some cost. The paid version of them came with support from their developer which is not a bad idea to have. One of the famous is called cPanel and it is well known in the web hosting industry. They offer different plans and it is worth the effort to take them into consideration as an option.
cPanel has a security advisor with a list of suggestions to check for hardening your operating system. This makes the process very easy in comparison with a vanilla implementation. Only click and follow the instructions and voila.
This security advisor will inform you if your system is out of date and it will recommend updating, or if your SSH password authentication is enabled then it will recommend disabling it, and so on.
ConfigServer Security and Firewall (csf)
This is a Stateful Packet Inspection (SPI) firewall, Login/Intrusion Detection, and Security application for Linux servers. It works out of the box in almost every Linux distribution in the market. It does not matter if it is a VPS or a Dedicated Server, it will work.

We recommend the use of this in any Linux implementation, and it does not matter if you are using a Web Control Panel or a Vanilla. CSF will install an extension in some of the Web Control Panels like cPanel and the Control Web Panel. If you are not using a Web Panel, then you can use the command line.
The ConfigServer has a suite of scripts that provides (the next is a copy-paste from their website, click here to redirect to the original text).
- Straight-forward SPI iptables firewall script.
- Daemon process that checks for login authentication failures for:
- Courier IMAP, Dovecot, UW-IMAP, Kerio.
- OpenSSH.
cPanel, WHM, Webmail (cPanel servers only). - Pure-ftpd, vsftpd, Proftpd.
- Password-protected web pages (htpasswd).
- Mod_security failures (v1 and v2).
- Suhosin failures.
- Exim SMTP AUTH.
- Custom login failures with separate log files and regular expression matching.
- POP3/IMAP login tracking to enforce logins per hour.
- SSH login notification.
- SU login notification.
- Excessive connection blocking.
- UI Integration for cPanel, DirectAdmin, InterWorx, CentOS Web Panel (CWP), VestaCP, CyberPanel, and Webmin.
- Easy upgrade between versions from within the control panel.
- Easy upgrade between versions from the shell.
- Pre-configured to work on a cPanel server with all the standard cPanel ports open.
- Pre-configured to work on a DirectAdmin server with all the standard DirectAdmin ports open.
- Auto-configures the SSH port if it's non-standard on installation.
- Block traffic on unused server IP addresses - helps reduce the risk to your server.
- Alert when end-user scripts send excessive emails per hour - for identifying spamming scripts.
- Suspicious process reporting - reports potential exploits running on the server.
- Excessive user process reporting.
- Excessive user process usage reporting and optional termination.
- Suspicious file reporting - reports potential exploit files in /tmp and similar directories.
- Directory and file watching - reports if a watched directory or file changes.
- Block traffic on a variety of Block Lists including DShield Block List and Spamhaus DROP List.
- BOGON packet protection.
- Pre-configured settings for Low, Medium, or High firewall security (cPanel servers only).
- Works with multiple ethernet devices.
- Server Security Check - Performs a basic security and settings check on the server (via cPanel/DirectAdmin/Webmin UI).
- Allow Dynamic DNS IP addresses - always allow your IP address even if it changes whenever you connect to the internet.
- Alert sent if server load average remains high for a specified length of time.
- mod_security log reporting (if installed).
Email relay tracking - tracks all emails sent through the server and issues alerts for excessive usage (cPanel servers only).
IDS (Intrusion Detection System) - the last line of detection alerts you to changes to system and application binaries.
SYN Flood protection. - Ping of death protection.
- Port Scan tracking and blocking.
- Permanent and Temporary (with TTL) IP blocking.
- Exploit checks.
- Account modification tracking - sends alerts if an account entry is modified, e.g. if the password is changed or the login shell.
- Shared Syslog aware.
- Messenger Service - This allows you to redirect connection requests from blocked IP addresses to preconfigured text and HTML pages to inform the visitor that they have been blocked in the firewall. This can be particularly useful for those with a large user base and help process support requests more efficiently.
- Country Code blocking - This allows you to deny or allow access by ISO Country Code.
- Port Flooding Detection - Per IP, per Port connection flooding detection and mitigation to help block DOS attacks.
- WHM root access notification (cPanel servers only).
- lfd Clustering - allows IP address blocks to be automatically propagated around a group of servers running lfd. It allows cluster-wide, removals and configuration changes.
- Quick start csf - deferred startup by lfd for servers with large block and/or allow lists.
- Distributed Login Failure Attack detection.
- Temporary IP allows (with TTL).
- IPv6 Support with ip6tables.
- Integrated UI - no need for a separate Control Panel or Apache to use the csf configuration.
Integrated support for cse within the Integrated UI. - cPanel Reseller access to per reseller configurable options Unblock, Deny, Allow, and Search IP address blocks.
- System Statistics - Basic graphs showing the performance of the server, e.g. Load Averages, CPU Usage, Memory Usage, etc.
- ipset support for large IP lists.
- Integrated with the CloudFlare Firewall.
- ...lots more!.
The copy-paste ends here.
You can't go wrong with the ConfigServer firewall.
Secure your Kernel. Ksplice, Kpatch, and Kernelcare
These are Linux kernel patching features built by different vendors. They all have similar features like the possibility of running live patching for running machines.
Once the feature is installed on your Linux machine, the kernel will get patches for vulnerabilities. One of the benefits is the application of patches in a reboot-less mode.
The machine will get the patches and continue the normal operation after that. Of course that in some cases you won't escape from a reboot but definitely it will increase the uptime of your services. You won't need to schedule any reboot or notified to any user about downtime coming.
Ksplice is an Oracle feature that is offered for distributions like Red Hat and Oracle Linux with Red Hat compatible kernels. Ksplice can patch glibc and openssl vulnerabilities without stopping applications and without interruption.
Kpatch is a Red Hat tool for Dynamic Kernel Patching in Red Hat distributions. This enables sysadmins to apply critical security patches to the kernel immediately, and the same as the rest of the vendors, without having to wait for long-running tasks to complete, users to log off, or scheduled reboot windows. It gives more control over uptime without sacrificing security or stability.
KernelCare, the last I mentioned from the list is the most used in the web hosting industry. It offers patching for the Linux kernel from almost all the distributions available on the market. AlmaLinux, CloudLinux, AWS, Centos, Debian, Oracle. Click here to see the complete list. Kernel care belongs to TuxCare and their whole business is related to security and extended life support for distributions that have reached the end of life.
From all these patching flavors we have our favorite and it is Kernelcare. They offer excellent support and it is very well known in the Web Hosting industry. It has been used and tested all around and it is a working feature with five stars.
CloudLinux for a secure shared environment
CloudLinux is a Linux distribution designed for a shared hosting environment and provides a modified Kernel based on OpenVZ. You probably have heard about VMware, KVM (Kernel-Based Virtual Machine)VirtualBox, Parallels, QEMU, Citrix, and others. These run the main OS as a Hypervisor.
The Hypervisor is the manager and administrator of virtual machines, and the virtual machines are like secure containers that run their own kernel and they have assigned resources, like memory and disc storage.
You can run different kernels inside the same Hypervisor but a difference between OpenVZ is that this will use replication of its own kernel to create containers. CloudLinux is an OpenVZ bases kernel and it will run at the top as any other operating system but with the advantage that it can run a Lightweight Virtual Environment (LVE) with its own resources like memory, CPU, input and output operations, and process without the overhead of a hypervisor.
It will create a secure and isolated environment for the users almost similar to a virtual machine. This environment is perfect for a shared hosting environment. You can assign memory, processor, and limit of the process to the users and create a very stable habitat for everybody.
As an example imagine you run a WordPress shared hosting with several accounts all having the same privileges. Every account uses the same quantity of processors and the same number of processes. Now imagine that one of these WordPress accounts is a successful one with an incredible amount of traffic, at some point this account will start eating all the resources, and a starving environment is then created. Other accounts start to feel the need for resources and everybody suffers the consequences.
With CloudLinux you will assign a limit to the resources an account can consume so there is no impact when one of them starts getting a hit of traffic. The only one who will be suffering is that specific account and not the whole community. The idea with this is that if an account is exceeding then we can place him in a different plan with more resources assigned to him if necessary but no one else will be affected during that time.
Another great plus for Cloulinux is the CageFS which is a virtualized, per-user file system that isolates all the accounts, preventing users from seeing each other and viewing sensitive information. With CageFS, Web Hosting providers avoid a large number of attacks, including privilege escalation and information disclosure attacks.
And for the last, CloudLinux works just wonderful with any Web Hosting Control Panel you decide to use.
Secure your data with a recovery plan against disasters
Thousands of companies from all around the world were affected, including governments, banks, web stores, and the game industry. Apparently, a failure in a UPS system got overheated and went on fire that extend to the entire facility. 500 ms square of equipment went to hashes.
That is not the only one, in 2014 the Samsung data center cough a major fire in South Korea. Not all is for fire. There are other elements like a water flood or lightning that can cause huge damage to facilities.
In the last few years, we have seen a huge increase in ransomware attacks, and we have seen what a terrorist attack can cause. There are so many factors that make it almost impossible to calculate the impact on our modern lives.
The best way to be protected and secure is to build your own recovery system against a disaster. Whatever you think would help then probably it would so do it. Take into consideration:
- How fast do you want to recover your data after an incident?
- Make a list of steps to follow and select the roles for your personal.
- Be able to identify the type of solution you require based on the type of disaster. If a war is coming, then it would be better to choose a different region or continent. Application failure, hardware failure, power failure, malware, ransomware, or natural disasters, just to mention some of them.
- Do not have your backups in the same location as your live data. Backups are your plan B and you want to make them as secure as possible. Choose a different country or data center facility for this.
- If possible make a double backup. A backup of your backup or a backup you can take with you to your fiscal storage place.
- Build a cluster of your services if possible. This way if one is down the other will go up with no losing time.
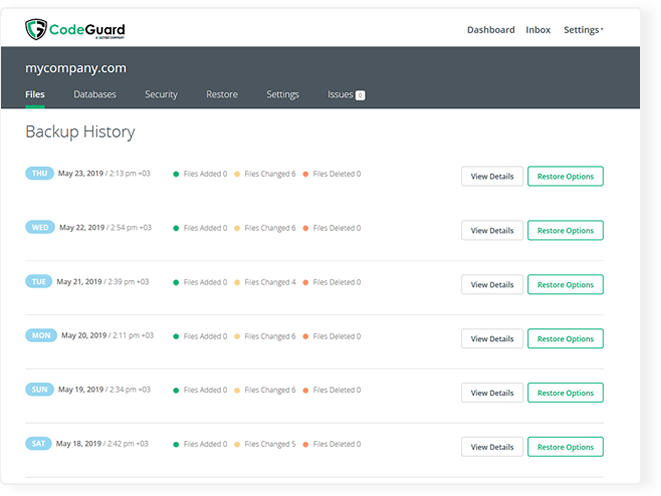
There are different backup options and solutions that you can use like Neteron Web Site Backups that let you choose to restore the whole account or just part of your files. This backup is powered by CodeGuard, a well-known security company called Sectigo. Your backup will be secured and saved encrypted and stored on Amazon Web Services Simple Storage System which provides market-leading resilience and redundancy for your backups.
There are other options and Neteron.com can help you build your own custom backup and anti-disaster solution. But as a minimum Codeguard should be taken into consideration for all its features and because it is very easy to use and implement.
Secure your Linux account against Malware
Linux is well known as a very secure operating system, no matter the distro you choose, it is going to be more secure than your Windows machine. This is because of the way it manages privileges, users, and ownerships. But this does not mean it is immune, it is not.

Web Hosting companies line neteron.com protect their systems by enforcing the Kerner, applying the last patches that cover the last treats, and using CloudLinux OS which isolates data leaks between the users.
The protection does not end there and there are threats at the user level. The combination that web hosting companies have to secure their infrastructure makes it possible to isolate the root and administrator process against threats that affect only users, keeping the malware running only in that specific account within a jail shell mode.
It is a standard let the user run the software they want to run and manage their account as they please, as it is not the Web Hosting Company to intervene in the user's account. It is the responsibility of the customer to keep their accounts clean of malware. The responsibility of the Web Hosting Company is to provide the necessary tools that the customer can use and execute to keep their account clean.
Neteron.com uses a partnership from SiteLock which comes through the WHMC license. This makes it possible to offer its customers a secure tool for fighting malware. Normally malware enters the user account through an unknown module installed in WordPress, or because the user did not know how to manage the permissions of its files and folders and let the threat enters his premises.
SiteLock will scan your sites for malware and vulnerabilities and let you know if something is found. There is a free version that will let you know if there is a threat in your files and there are plans that will not only find the code but will remove it.
Depending on your website security package, you’ll receive daily website scans, automated malware removal, vulnerability/CMS patching, as well as a web application firewall to block harmful traffic before it ever reaches your site.

But what happens when your account is hacked?
We never expected to get haked and when this happened we usually get into a first panic stage, where we are trying to understand how this happened.
Do not panic. There are a couple of steps you can do to fix it.
- If you get hacked because you installed some unknown software, you can always go back to an older backup, one that is clean.
- Another solution is if your website has been attacked and compromised you can get immediate emergency assistance to quickly recover your site using SiteLock emergency response.
- Get the fastest response time with analysis and work to recover your site started within 30 minutes.
- If the automatic technology is unable to remove the malicious content then real people will perform manual cleaning.
- With the emergency package, you get fast-tracked straight to the top of the queue.
- SiteLock will continue to monitor your site for 7 days to ensure that your site remains malware-free post-recovery.
- The emergency service is available for a single one-off fee, there are no recurring fees or subscriptions.
- If you are using WordPress you can use some of the secure WordFense premium protection plans which include Malware Removal, Incident Response, Blocklist Removal, and Search Cleanup. WordFense is a real deal in security for WordPress.
Keep your emails secure and free of spam
This happened to all of us, once we have our own email box configured everything looks just fine, but the time goes by and little to little we start getting spam, garbage, and some very dangerous emails from unknown senders and fishing content or malware in the attachments.
It was worse a few years ago but the industry has been fighting this and nowadays there lot of vendors and thousands of implementation of email security appliances everywhere, at all levels.

These appliances get database updates, new string sets, and new regular expressions that look for patterns and check the headers of the email for familiar matches and mark them as spam.
Email security starts from your domain records. Configuring the mail services is a little more complicated than just creating your first email account. You must secure it with the best practices and configure the next values:
- DKIM (Domain Keys Identified Mail): is an email authentication technique that allows the receiver to check that an email was indeed sent and authorized by the owner of that domain.
- SPF (Sender Policy Framework): is an email authentication method designed to detect forging sender addresses during the delivery of the email.
One is used for senders and the other is used by receivers, and because emails send and receive then you must configure both of the.
You could use a Spam Filter engine, like SpamAssassin for your email accounts, this will help you to identify unsolicited bulk emails (spam), and send them to a separate folder (Spam Box) or automatically delete them (Auto-Delete) from your email account.
SpamAssassin uses a variety of security mechanisms including header and text analysis, Bayesian filtering, DNS blocklists, and collaborative filtering databases. SpamAssassin runs on a server, and filters spam before it reaches your mailbox. The configuration can be tuned but it requires some effort from you.
Another very easy solution that you can deploy is called SpamExpert. This is the easiest way to keep clean your inbox from spam and more.
This security feature is very easy to configure and it will start working immediately, you will notice the difference. It will detect 99% of the unwanted emails and it will scan your emails for malware. This is a two-in-one feature, and for the price, it is worth it.
With SpamExpert your emails will be received in the correct inbox folder of your recipients, and your inbox will stay clean from unwanted emails. This technology is maintained and tuned all the time, no need for your intervention.
You will benefit from a rich array of features, via a user-friendly interface with multilevel control, live quarantine, and regular new releases. The solution offers multilevel control and additional email continuity via storing emails and retrying delivery during outages or downtime. This is a serious feature, at the same level as the major leagues in emails but for a very affordable price here.

Secure your access using a VPN
Here is nothing more uncomfortable than getting locked from your own server. This has happened to all of us and one of the options to work over this is using a VPN to re-connect and clean your IP from the firewall black list.
You can use any VPN service or you can get the cheapest Virtual Private Server and install OpenVPN there. This is a free-to-use, secure and open-source VPN solution. The free-to-use version is limited to two connections simultaneously.
If you use your own VPN application you will have the advantage that you can add the VPN IP address to the whitelist of your server firewall, and this IP won't change during the time you have the VPN.
This will give you secure access at any time and from anywhere. You establish a connection to your VPN and after that, your access to your server is always granted as the IP address is already whitelisted. This is useful when you have strict rules that are easily violated even by trustful networks. This can happen when your network uses a dynamic IP address to the internet.
Neteron.com has a secure VPN feature that you can get and encrypt your traffic with high speed, security, and easy to use with instant setup. This is an unlimited usage in a high-speed network. You won't be disappointed knowing that just one subscription covers and protects up to 5 devices simultaneously.
Conclusion
There are a lot of easy-to-deploy features that are made for securing your infrastructure. You should consider all the options and pick up the one that you need. Nowadays there are no excuses for having your infrastructure unprotected.
The End.